Trezor Login: Effortless & Secure Crypto Access
Learn the safest way to log in to your Trezor wallet, manage your cryptocurrency portfolio, and safeguard your assets with trusted hardware security.
What is Trezor Login?
Trezor login is the secure access point for your Trezor hardware wallet. It allows you to view balances, send and receive cryptocurrencies, and manage private keys safely offline, away from online threats.
Benefits of Using Trezor Login
- Private keys remain offline and secure
- Approve transactions directly on the device
- Support for multiple cryptocurrencies
- Monitor portfolio and activity via Trezor Suite
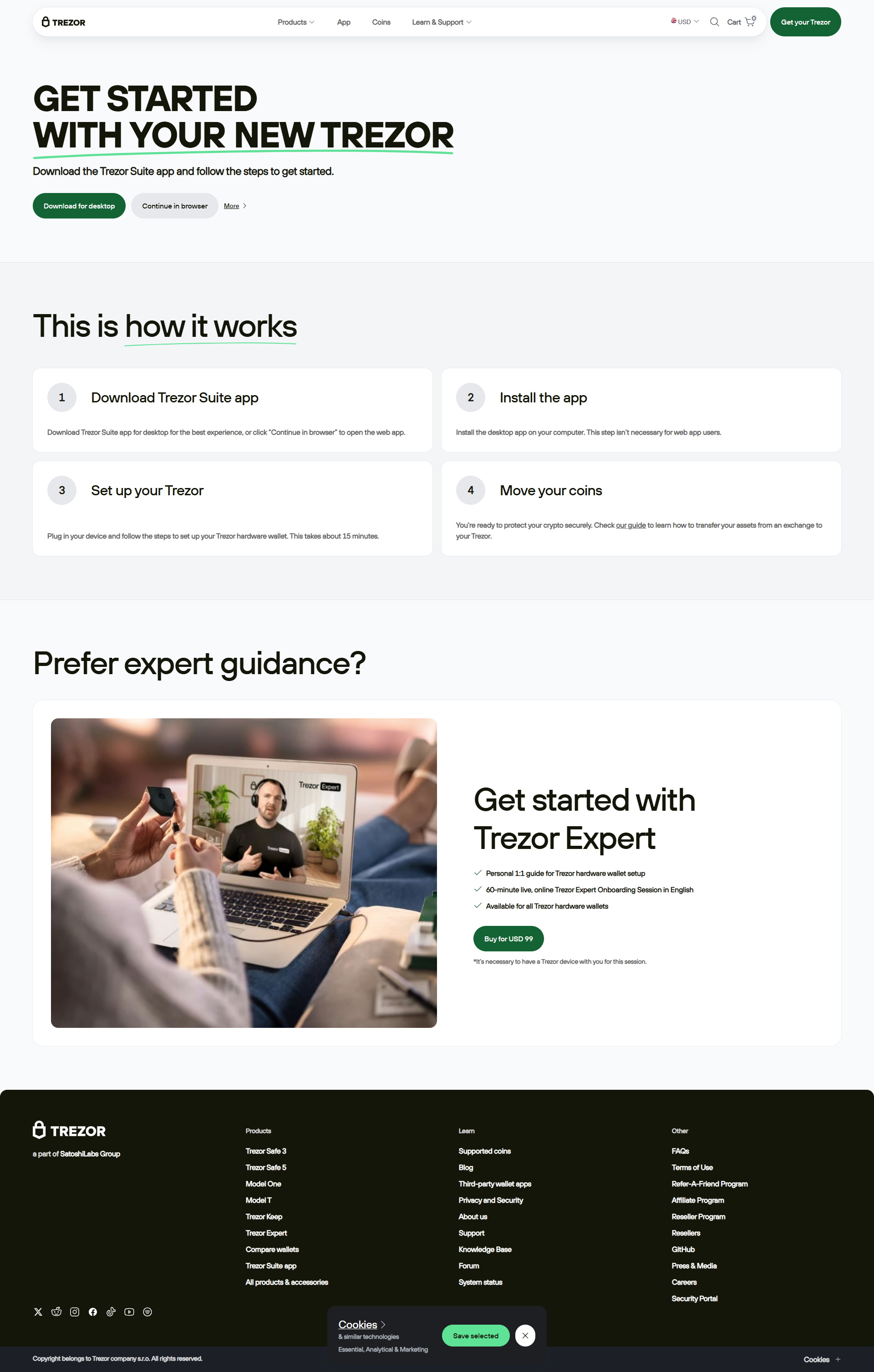
Step-by-Step Trezor Login
- Connect Device: Plug in your Trezor using USB or compatible connection.
- Open Trezor Suite: Launch the official desktop or web application.
- Enter PIN: Input securely on your Trezor device.
- Access Wallet: View balances, send/receive funds, and manage your assets.
- Confirm Transactions: Approve directly on the hardware device for safety.
- Log Out: Close the Suite and safely disconnect your device.
🔒 Security Tips
Always use official Trezor Suite or verified web apps. Never input your recovery phrase online and confirm all transactions directly on the hardware device.
Trezor Login vs Third-Party Access
| Feature | Official Trezor Login | Third-Party Apps |
|---|---|---|
| Security | Private keys offline; PIN required | Higher risk of phishing or malware |
| Authenticity | Verified via Trezor Suite | May be unverified or fake |
| Ease of Use | Beginner-friendly guided steps | Varies; may be confusing |
| Recommended Users | All Trezor users | Advanced users only |
Troubleshooting Trezor Login
Device Not Detected
Reconnect the device, restart Trezor Suite, and verify firmware is up-to-date.
Forgot PIN
Reset the device using your recovery phrase and set a new PIN.
Suite Loading Issues
Restart your computer, close conflicting applications, and update to the latest Trezor Suite.
Trezor Login Checklist
- ✅ Connect your Trezor device
- ✅ Open official Trezor Suite
- ✅ Enter PIN securely
- ✅ Manage your crypto safely
- ✅ Log out and disconnect after use
Conclusion
Logging in through Trezor login ensures maximum security for your cryptocurrencies. By following official procedures, confirming transactions on the device, and staying vigilant, you maintain full control over your digital assets safely and confidently.